User Activity Documentation Covering Anoceligt and Alerts Logs
User activity documentation plays a critical role in enhancing security and understanding user behavior within digital environments. Anoceligt logs offer a detailed account of user interactions, while alerts logs provide insights into system performance and potential security threats. Together, these logs form a comprehensive framework for analyzing user activity. However, the effectiveness of this documentation hinges on the application of best practices. What strategies can organizations implement to maximize the benefits of this data?
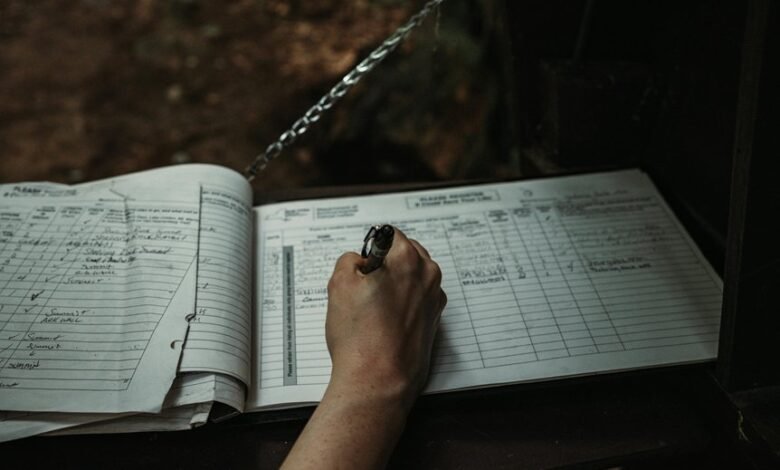
Importance of User Activity Documentation
Although often overlooked, the importance of user activity documentation cannot be understated in the context of modern digital environments.
Effective documentation strategies facilitate the understanding of user behavior, allowing organizations to enhance user experiences and improve security measures.
Understanding Anoceligt Logs
Anoceligt logs serve as crucial records that capture user activity within a digital environment, providing a comprehensive overview of interactions and behaviors.
Understanding anoceligt definitions is essential for effective log interpretation, enabling users to discern patterns and anomalies.
Analyzing Alerts Logs
Alerts logs provide a vital layer of insight into system performance and potential security incidents.
By identifying alert patterns, analysts can discern normal behavior from log anomalies, highlighting areas requiring attention. This examination not only aids in immediate issue resolution but also contributes to long-term security strategies.
Understanding these logs empowers organizations to maintain autonomy while safeguarding their digital environments against emerging threats.
Best Practices for Leveraging User Activity Data
To effectively leverage user activity data, organizations must adopt a systematic approach that prioritizes data integrity and relevance. This involves tracking user behavior meticulously to identify patterns and anomalies.
Additionally, implementing robust analytical tools enhances data security by enabling proactive measures against potential threats. By aligning these practices, organizations can harness user activity data to foster a secure and responsive environment.
Conclusion
In conclusion, the meticulous documentation of user activity through anoceligt and alerts logs is indispensable for organizations aiming to enhance security and user experience. While some may argue that such extensive monitoring invades user privacy, it is essential to recognize that these logs not only safeguard sensitive information but also empower organizations to identify and mitigate potential threats proactively. Thus, a balanced approach to user activity documentation fosters both security and trust within digital environments.





